Chiavi di Sicurezza
Protects against the following threat(s):
Una chiave di sicurezza fisica aggiunge un livello di protezione molto forte ai tuoi account online. Compared to authenticator apps, the FIDO2 security key protocol is immune to phishing, and cannot be compromised without physical possession of the key itself. Many services support FIDO2/WebAuthn as a multi-factor authentication option for securing your account, and some services allow you to use a security key as a strong single-factor authenticator with passwordless authentication.
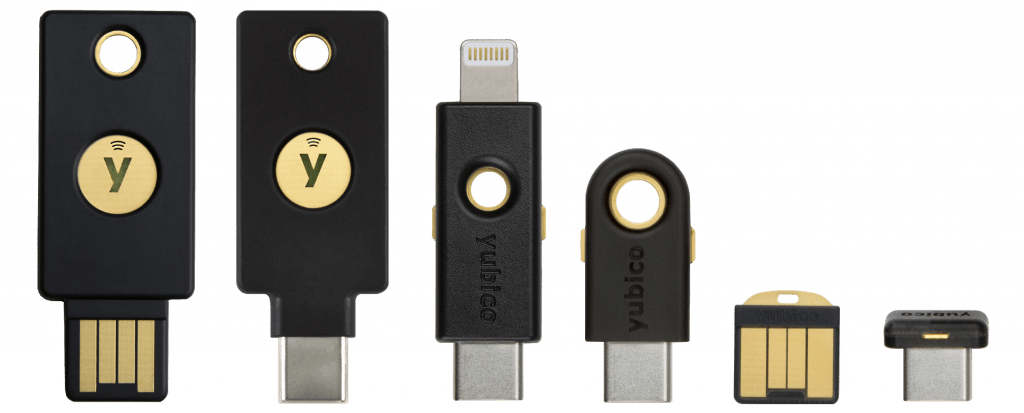
Yubico Security Key

La serie Yubico Security Key è la chiave di sicurezza hardware più conveniente con certificazione FIDO di livello 2. Supporta FIDO2/WebAuthn e FIDO U2F e funziona con la maggior parte dei servizi che supportano una chiave di sicurezza come secondo fattore, nonché con molti gestori di password.
These keys are available in both USB-C and USB-A variants, and both options support NFC for use with a mobile device as well.
This key provides only basic FIDO2 functionality, but for most people that is all you will need. Some notable features the Security Key series does not have include:
- Yubico Authenticator
- CCID Smart Card support (PIV-compatibile)
- OpenPGP
If you need any of those features, you should consider their higher-end YubiKey of products instead.
Avviso
The firmware of Yubico's Security Keys is not updatable. If you want features in newer firmware versions, or if there is a vulnerability in the firmware version you are using, you would need to purchase a new key.
YubiKey
The YubiKey series from Yubico are among the most popular security keys. The YubiKey 5 Series has a wide range of features such as: Universal 2nd Factor (U2F), FIDO2 and WebAuthn, Yubico OTP, Personal Identity Verification (PIV), OpenPGP, TOTP and HOTP authentication.
The comparison table shows the features and how the YubiKeys compare to each other and to Yubico's Security Key series. One of the benefits of the YubiKey series is that one key can do almost everything you could expect from a hardware security key. We encourage you to take their quiz before purchasing in order to make sure you make the right choice.
The Yubikey 5 series has FIDO Level 1 certification, which is the most common. However, some governments or other organizations may require a key with Level 2 certification, in which case you'll have to purchase a Yubikey 5 FIPS series key, or a Yubico Security Key. Most people do not have to worry about this distinction.
YubiKeys can be programmed using the YubiKey Manager or YubiKey Personalization Tools. For managing TOTP codes, you can use the Yubico Authenticator. All of Yubico's clients are open source.
For models which support HOTP and TOTP, there are 2 slots in the OTP interface which could be used for HOTP and 32 slots to store TOTP secrets. These secrets are stored encrypted on the key and never expose them to the devices they are plugged into. Once a seed (shared secret) is given to the Yubico Authenticator, it will only give out the six-digit codes, but never the seed. This security model helps limit what an attacker can do if they compromise one of the devices running the Yubico Authenticator and make the YubiKey resistant to a physical attacker.
Avviso
The firmware of YubiKey is not updatable. If you want features in newer firmware versions, or if there is a vulnerability in the firmware version you are using, you would need to purchase a new key.
Nitrokey

Nitrokey has a security key capable of FIDO2 and WebAuthn called the Nitrokey FIDO2. For PGP support, you need to purchase one of their other keys such as the Nitrokey Start, Nitrokey Pro 2 or the Nitrokey Storage 2.
The comparison table shows the features and how the Nitrokey models compare. The Nitrokey 3 listed will have a combined feature set.
Nitrokey models can be configured using the Nitrokey app.
For the models which support HOTP and TOTP, there are 3 slots for HOTP and 15 for TOTP. Some Nitrokeys can act as a password manager. They can store 16 different credentials and encrypt them using the same password as the OpenPGP interface.
Avviso
While Nitrokeys do not release the HOTP/TOTP secrets to the device they are plugged into, the HOTP and TOTP storage is not encrypted and is vulnerable to physical attacks. If you are looking to store HOTP or TOTP secrets, we highly recommend that you use a YubiKey instead.
Avviso
Resetting the OpenPGP interface on a Nitrokey will also make the password database inaccessible.
Criteri
Please note we are not affiliated with any of the projects we recommend. In addition to our standard criteria, we have developed a clear set of requirements to allow us to provide objective recommendations. Ti suggeriamo di familiarizzare con questo elenco prima di scegliere di utilizzare un progetto e di condurre le tue ricerche per assicurarti che si tratti della scelta adatta a te.
Requisiti minimi
- Must use high quality, tamper resistant hardware security modules.
- Must support the latest FIDO2 specification.
- Must not allow private key extraction.
- Devices which cost over $35 must support handling OpenPGP and S/MIME.
Caso migliore
I nostri criteri ottimali rappresentano ciò che vorremmo vedere dal progetto perfetto in questa categoria. I nostri consigli potrebbero non includere tutte o alcune di queste funzionalità, ma quelli che le includono potrebbero essere preferiti ad altri su questa pagina.
- Should be available in USB-C form-factor.
- Should be available with NFC.
- Should support TOTP secret storage.
- Should support secure firmware updates.
Stai visualizzando la copia in Italiano di Privacy Guides, tradotta dal nostro fantastico team di lingue su Crowdin. Se noti un errore, o vedi eventuali sezioni non tradotte in questa pagina, considerare di dare una mano! Visita Crowdin
You're viewing the Italian copy of Privacy Guides, translated by our fantastic language team on Crowdin. If you notice an error, or see any untranslated sections on this page, please consider helping out!